Voice traffic often travels over the public internet. An SBC ensures those calls are authenticated, encrypted, properly routed, and protected from fraud or attacks.
If your business uses VoIP, an SBC is the component that keeps your voice communication secure, stable, and compliant.
What Is an SBC (Session Border Controller)?
A Session Border Controller (SBC) is a network device or software application that manages and secures voice communication sessions—such as VoIP calls—at the boundary of a network. It sits between your internal phone system (like a PBX or unified communications platform) and external networks, including the public internet or a SIP trunk provider.
In simple terms, an SBC acts as a security and control layer for SIP-based voice traffic. It protects your phone system from external threats, ensures proper call routing, enforces communication policies, and maintains call quality across network boundaries.
If your organization uses VoIP, SIP trunking, or hybrid cloud telephony, an SBC plays a critical role in keeping voice communication secure, reliable, and compliant.
How Does an SBC Work?
A Session Border Controller operates at the edge of your network, controlling how voice sessions enter and leave your infrastructure. It monitors and manages SIP signaling and media traffic before allowing calls to pass through.
Here’s a simplified step-by-step view of how it works:
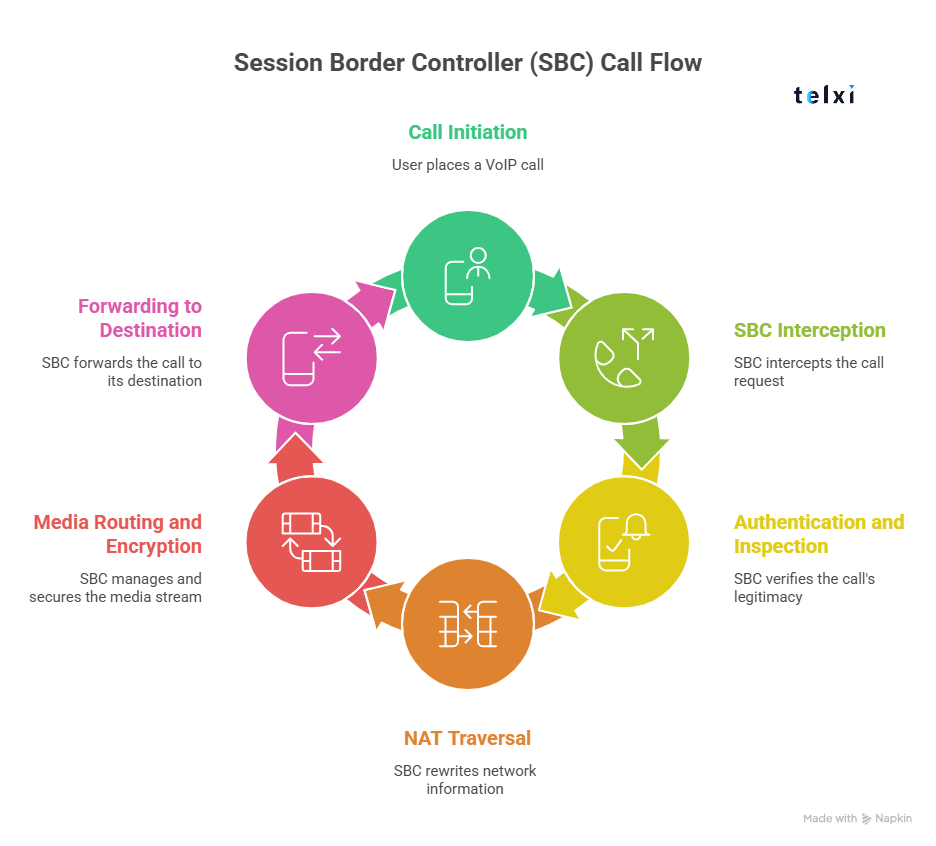
1. Call is initiated (SIP signaling)
When a user places a VoIP call, a SIP signaling request is sent from the internal phone system (PBX or cloud platform) toward the external network.
This signaling contains information about the caller, destination, codecs, and session parameters.
2. SBC intercepts traffic at the network edge
Instead of allowing that traffic to go directly to the internet or SIP provider, the SBC sits in between and intercepts the request.
This “border” position is what gives it control over the session.
3. Authentication and inspection
The SBC verifies that the request is legitimate. It checks:
-
User credentials
-
IP address validity
-
SIP header structure
-
Policy compliance
It can block malformed or suspicious traffic to prevent fraud or attacks.
4. NAT traversal
Many internal phone systems operate behind firewalls using private IP addresses. The SBC rewrites network information so that SIP packets can correctly traverse Network Address Translation (NAT).
Without this step, audio may fail, or calls may not connect properly.
5. Media routing and encryption
Once signaling is validated, the SBC manages the media stream (voice traffic). It can:
-
Encrypt audio using TLS/SRTP
-
Select compatible codecs
-
Optimize routing paths
-
Apply bandwidth controls
This ensures secure and high-quality audio transmission.
6. Forwarding to the destination
After validation and processing, the SBC forwards the call to its destination—either:
-
A SIP trunk provider
-
Another enterprise network
-
A cloud communication platform
Throughout the session, the SBC continues to monitor the call to enforce policies and protect against disruptions.
What Does an SBC Do?
A Session Border Controller performs several critical functions to secure, manage, and optimize voice sessions that cross your network boundary. It acts as a security layer, traffic controller, and compatibility manager for SIP-based communications.
Below are the core functions of an SBC:
-
SIP message validation — Inspects SIP signaling packets to ensure they are correctly formatted and authorized. Blocks malformed or suspicious requests before they reach your internal systems.
-
Encryption (TLS / SRTP) — Secures signaling with TLS and encrypts media streams using SRTP to protect voice traffic from interception or tampering.
-
NAT traversal — Rewrites IP address information so that internal systems behind firewalls (using private IPs) can communicate properly with external networks.
-
Topology hiding — Masks internal IP addresses, extensions, and network structure to prevent external parties from mapping your infrastructure.
-
Fraud prevention — Detects unusual call patterns, unauthorized access attempts, and suspicious international dialing activity to reduce toll fraud risk.
-
DoS / DDoS mitigation — Monitors traffic volume and behavior to identify and block denial-of-service attacks that could disrupt voice services.
-
Call admission control — Limits the number of concurrent sessions allowed through the system to prevent overload and maintain call quality.
-
Protocol normalization — Adjusts SIP headers and signaling details to ensure compatibility between different vendors and carriers.
-
Interoperability management — Enables communication between various PBX systems, SIP trunk providers, and cloud platforms by enforcing consistent signaling behavior.
Why Is an SBC Important for SIP Trunking?
When using SIP trunking, your phone system connects directly to external networks over the internet. Without proper protection, your PBX can become exposed to security risks, fraud, and service disruptions. This is where a Session Border Controller becomes essential.
An SBC protects your voice infrastructure in several important ways:
-
Protects the PBX from direct internet exposure — The SBC sits at the network edge, preventing external traffic from directly accessing your internal phone system.
-
Prevents toll fraud — By monitoring and validating SIP traffic, the SBC blocks unauthorized call attempts and suspicious international dialing patterns.
-
Ensures secure routing — It encrypts signaling and media traffic while enforcing authentication and policy controls.
-
Maintains call quality — Through call admission control and traffic management, the SBC helps prevent overload and supports stable audio performance.
-
Meets enterprise security standards — In many corporate and regulated environments, deploying an SBC is considered a best practice for SIP trunk security.
SBC vs Firewall vs Router
An SBC is specifically designed for voice traffic, while firewalls and routers focus on general network security and data routing. A firewall and router protect and route general network traffic, while an SBC specifically protects and manages VoIP communication.
| Feature | SBC | Firewall | Router |
|---|---|---|---|
| Protects VoIP signaling | Yes | Limited | No |
| Handles SIP protocol | Yes | No | No |
| Media encryption (TLS/SRTP) | Yes | No | No |
| Network routing | Limited | No | Yes |
What’s the difference?
-
A Session Border Controller (SBC) is purpose-built to manage and secure SIP-based voice sessions. It understands VoIP protocols and actively controls call behavior.
-
A firewall filters general network traffic based on IP addresses, ports, and security rules—but it does not understand SIP signaling in depth.
-
A router directs network traffic between systems but does not provide SIP-level security or voice session management.
Types of SBCs
Session Border Controllers can be deployed in different ways depending on your infrastructure, scale, and operational model. The three main types are hardware, virtual, and cloud-based SBCs.
-
Hardware-based SBC — A physical appliance installed on-premises within a company’s data center or server room. Typically used by large enterprises, telecom operators, and organizations with strict compliance or high-volume voice environments that require dedicated infrastructure.
-
Virtual SBC — A software-based SBC deployed on virtual machines within private data centers or virtualized environments. Often used by mid-sized businesses and enterprises that want flexibility without purchasing dedicated hardware.
-
Cloud SBC — A cloud-hosted SBC delivered as a service, usually integrated into cloud PBX or unified communications platforms. Common among remote-first companies, SMBs, and organizations adopting cloud telephony.
Example of an SBC in Action
« Back to Glossary IndexImagine a company using a SIP trunk to handle inbound customer support calls.
When a call comes in from the public network, it first reaches the Session Border Controller at the edge of the company’s infrastructure. The SBC inspects the SIP signaling to verify that the request is legitimate and properly formatted.
If the traffic appears suspicious—such as malformed SIP headers or unusual international dialing patterns—the SBC blocks the call before it reaches the internal PBX. This prevents potential fraud or service disruption.
If the call is valid, the SBC securely routes it to the correct destination, such as a support queue or extension, while applying encryption and policy controls.
In this way, the SBC acts as a security gatekeeper—allowing legitimate calls through while protecting the internal voice system from threats.